Cloud computing has become a popular choice for many businesses, resulting in outsourcing becoming more common in the accounting industry. Additionally, telecommuting is now a regular practice, even for after-hours tasks. However, amidst these trends, it’s critical not to overlook the importance of implementing strong security measures to safeguard sensitive data. So, what steps can you take to ensure the protection of your valuable information?
Timed Lockout
It is highly recommended to implement a timed lockout mechanism for all user access. This security measure involves allowing users three login attempts, and if they fail to log in successfully within those attempts, the system will automatically lock them out for a period of one hour. This strategy serves as an effective deterrent against hackers and can be implemented as part of a comprehensive Intrusion Detection System.
Passwords
Always have passwords as a mix of numbers, letters and symbols.
You may be interested in hack times released by an anti-virus software company – note the speed at which passwords with words are hacked:
myThomas9876543 – 3.6 seconds
Martin8569 – 12.01 seconds
21Everest – 2 minutes
mammamia – 3 minutes
896rUU – 2 hours Please note the above is WITHOUT the timed lockout feature we have mentioned which means hacking software would take months or even years to hack a system if the password is the last one.
Furthermore, a username can possess the same level of complexity as a password, rather than being simply a name, in order to further enhance its security.
A way of creating a password is to use a sentence and take the first letter of each word and substitute “$” for the letter “S” and any other substitutions you will easily remember. E.g. My first house was at 11 Bunning Street
Would give a password: Mfhw@11B$
It is not advised to transmit passwords through email or instant messaging services. We highly recommend sharing passwords verbally or sending them through text messages as a more secure method.
We recommend offering users the option to change their password upon initial login, in accordance with our guidelines. Additionally, we suggest implementing a password expiry notification system to prompt regular password changes.
Restrict Access
If you utilise a server, it is crucial to establish permissions and limit accessibility. This process can be easily handled by an IT contractor to ensure proper security measures. Typically, only the IT Administrator should possess administrative rights such as the ability to delete program files. Depending on your company’s structure, file deletion privileges should be reserved for individuals who genuinely require this capability. At minimum, remote users should be denied permission to delete files, folders, and software from the server. For enhanced control, permissions should be set for each folder on your hard drive in order to define access rights for different individuals or groups. It is also advisable to restrict access to system or application root files. Additionally, if your accounting software offers the feature, consider restricting access to individual client files only to those who truly necessitate entry into a specific file.
Final Note
It is crucial to consistently perform daily backups and to update passwords whenever staff changes occur.
At BOSS, we prioritise the implementation of rigorous security protocols. Furthermore, we have gone above and beyond by taking additional measures to enhance security and maintain confidentiality. Our clients’ data is highly important to us, and we have taken every reasonable precaution to ensure its safety in our capable hands.
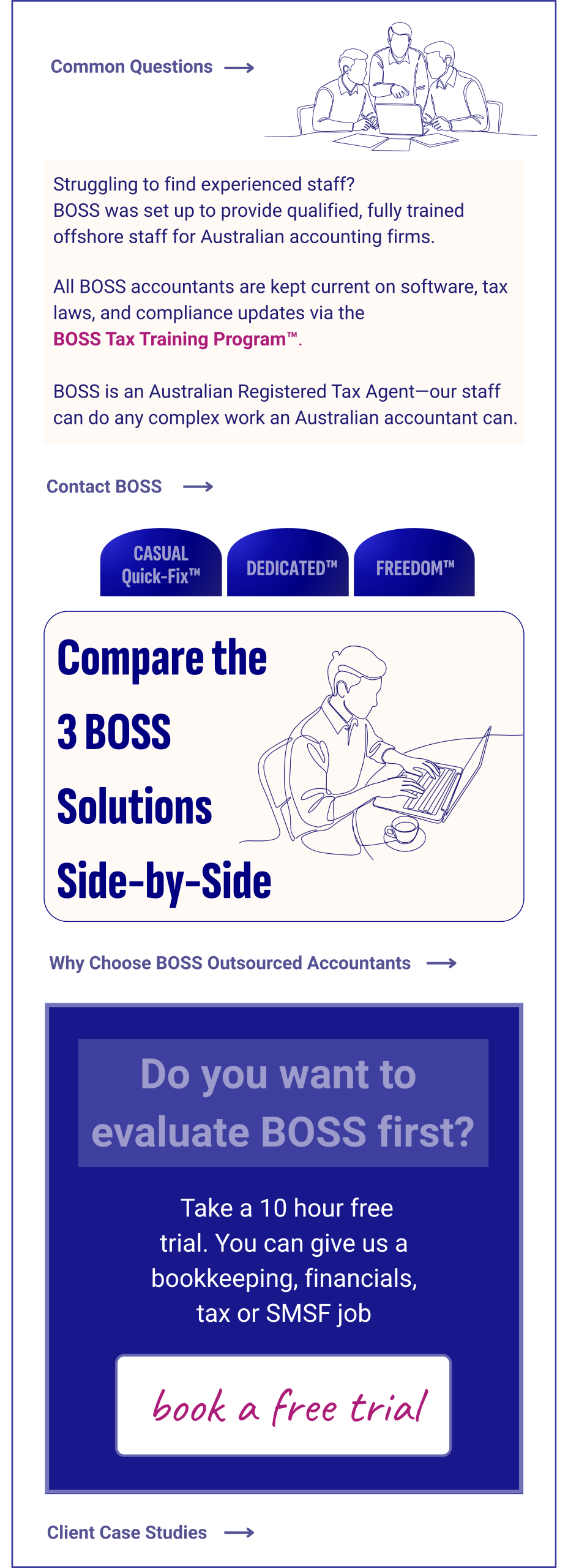
Now that you have gained a better understanding of the calibre of an outsourcing provider that we are, why not take advantage of our offer for a free trial?